Blog
The BoxyHQ blog is where our team shares our thoughts and ideas about everything from our products to industry news and insights. We also welcome guest posts so please do get in touch if you have any thoughts you would like to share on our blog.
Security Update: Addressing XML Signature Verification Vulnerabilities

Co-founder & CEO @BoxyHQ
Asegurando la IA y los LLM: El Papel Crítico de los Controles de Acceso

Co-founder & COO @BoxyHQ
Securing AI and LLM: The Critical Role of Access Controls

Co-founder & COO @BoxyHQ
Understanding Prompt Injection: A Growing Concern in AI and LLM

Co-founder & COO @BoxyHQ
What is a SaaS Starter Kit? 5 Things to Consider Before Choosing One

Co-founder & COO @BoxyHQ
AI Audit Logs: The Secret Weapon to Enhance Enterprise Security

Co-founder & COO @BoxyHQ
Simplifying Identity Management: The Power of Identity Federation

Co-founder & COO @BoxyHQ
How Effortless Solutions Managed Multi-Tiered Client Needs with BoxyHQ SSO

Customer Success, Community, DevRel - @BoxyHQ
The Build vs Buy Conundrum: Identity, Access, and Identity Federation Solutions

Customer Success, Community, DevRel - @BoxyHQ
Achieving Seamless SSO Integration: Why BlockSurvey Selected BoxyHQ

Customer Success, Community, DevRel - @BoxyHQ
Leveraging BoxyHQ’s Open-Source SSO for Greater Market Reach and Compliance: MonkeyFit

Customer Success, Community, DevRel - @BoxyHQ
What is SAML and why you should care

Customer Success, Community, DevRel - @BoxyHQ
Unlocking Efficiency with Enterprise SSO: A Unosecur Case Study

Customer Success, Community, DevRel - @BoxyHQ
BoxyHQ Changelog, January 2024: SAML Jackson, Retraced, and More

Customer Success, Community, DevRel - @BoxyHQ
BoxyHQ 2023 Changelog: Enhancing Security with Retraced-Powered Audit Logs

Customer Success, Community, DevRel - @BoxyHQ
BoxyHQ Changelog: Transforming Enterprise SSO and Directory Sync in 2023 with SAML Jackson

Customer Success, Community, DevRel - @BoxyHQ
Progress and Challenges in Securing The Web Ecosystem in 2023 - A Year in Review

Customer Success, Community, DevRel - @BoxyHQ
Unlocking Business Growth: A Conversation with Dub's Founder

Community Engineer @BoxyHQ
Unicis.Tech Unlocks Security: A Conversation with the Founder

Community Engineer @BoxyHQ
Boosting Trust and Efficiency: A Conversation with Supademo's CEO

Community Engineer @BoxyHQ
🧭 Navigating the Open Source Landscape: ⭐Finding Your First Contribution

Community Success Engineer @BoxyHQ
Interview with Cal.com: Enhancing Enterprise Experience with BoxyHQ

Community Success Engineer @BoxyHQ
Transforming Security and Access: A Conversation with the Spike Team

Community Success Engineer @BoxyHQ
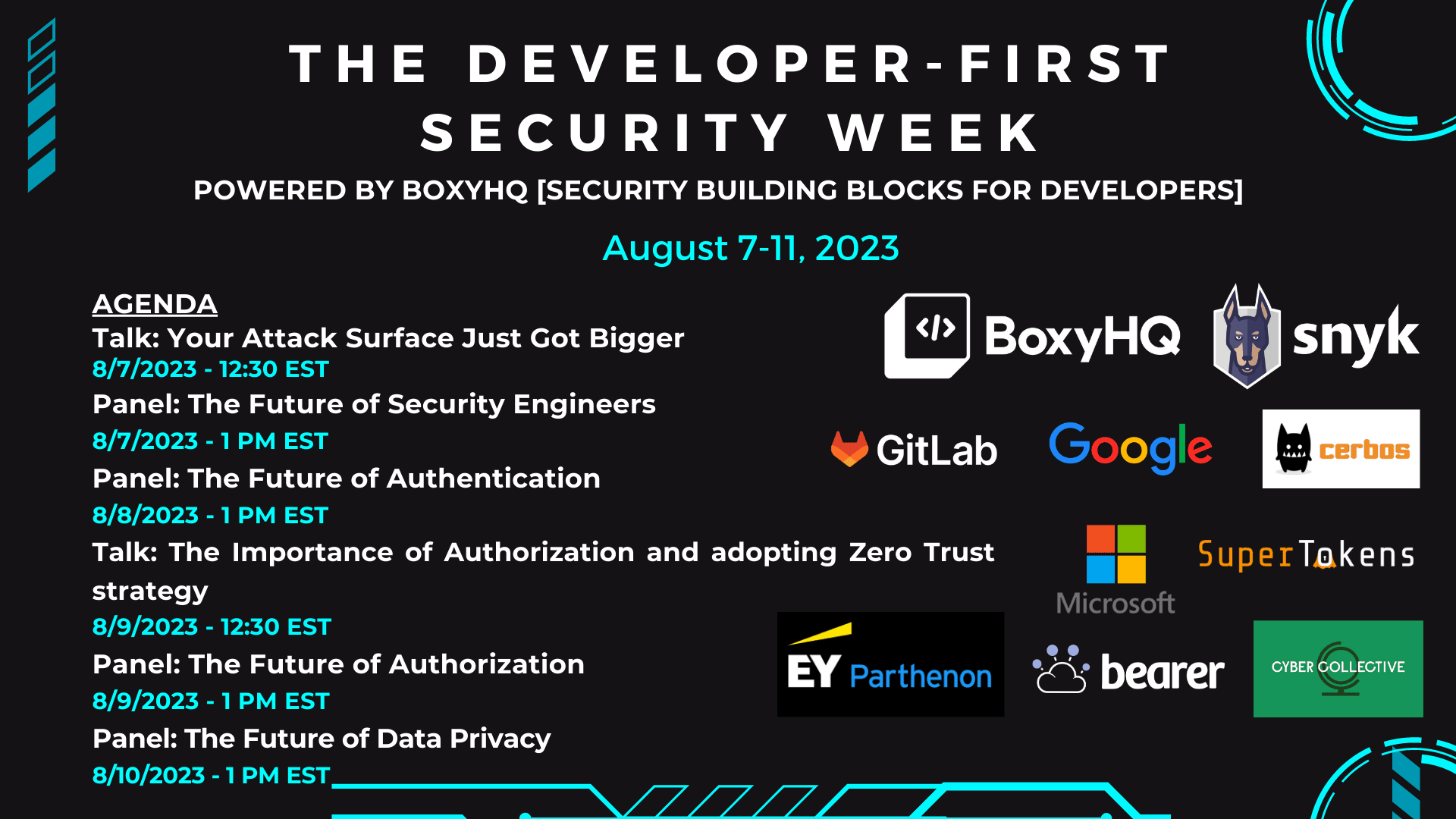
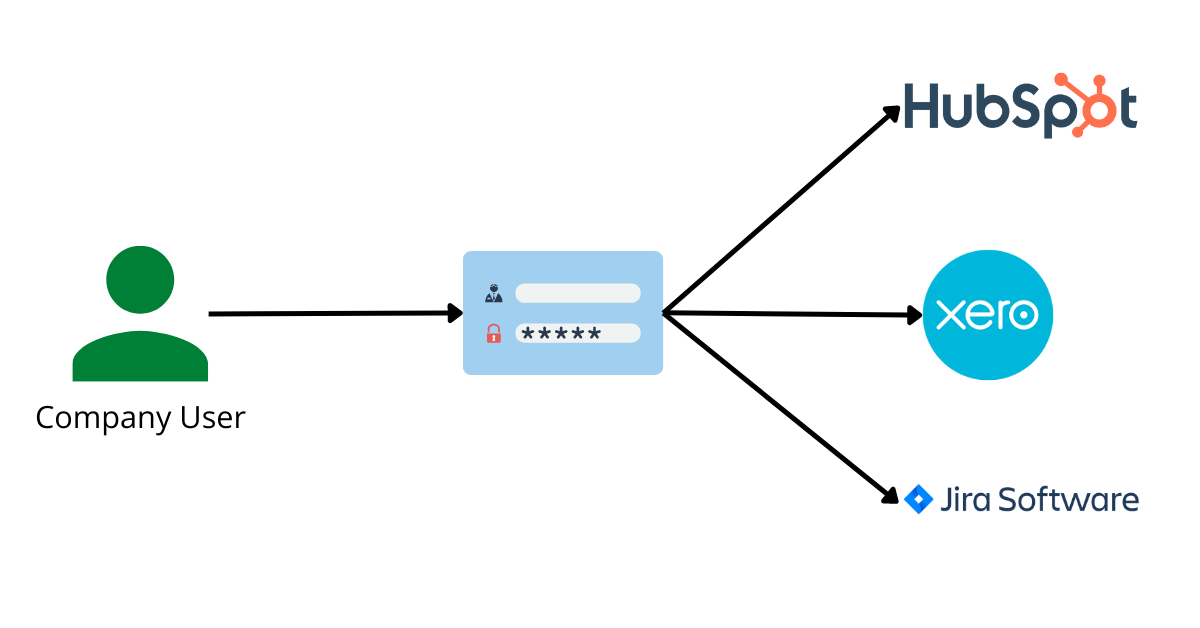
BoxyHQ + Cerbos: Merging SSO and Authorization

Senior Developer @ BoxyHQ
BoxyHQ - The must-have for your startup's next enterprise customer

Content & Marketing Head @Scoutflo
Ignite Your SaaS Journey with the Best Free and Open-Source SaaS Starter Kit

Co-founder & COO @BoxyHQ
Build Enterprise Software with No-Code Thanks to Bubble.io

Community Success Engineer @BoxyHQ
SBOM Explained: An enterprise guide to security risk management

Community Success Engineer @BoxyHQ
Exploring the open-source business model and how companies monetize it

Co-founder & CEO @BoxyHQ
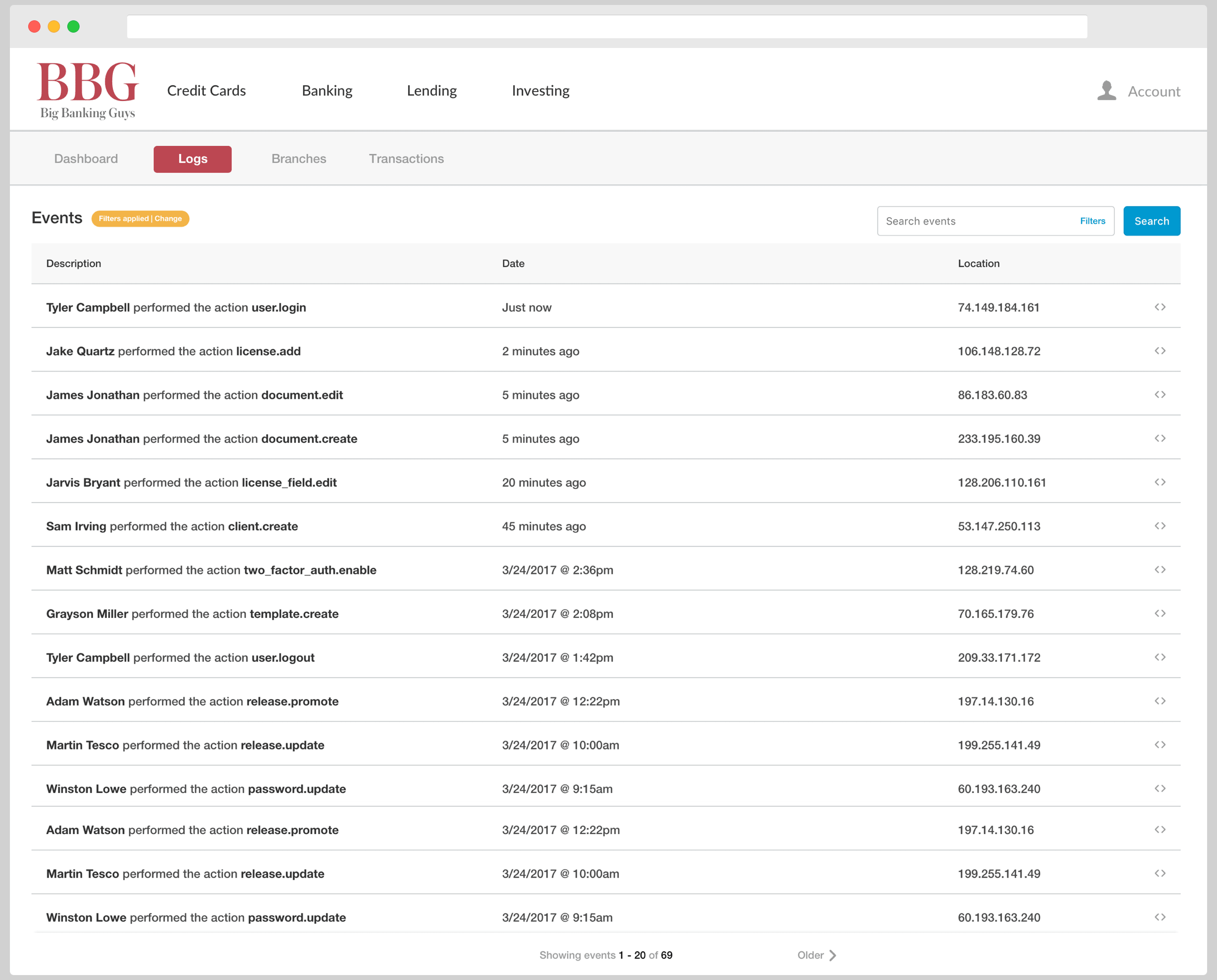
Why does your SaaS application need audit logs?

Co-founder & CEO @BoxyHQ
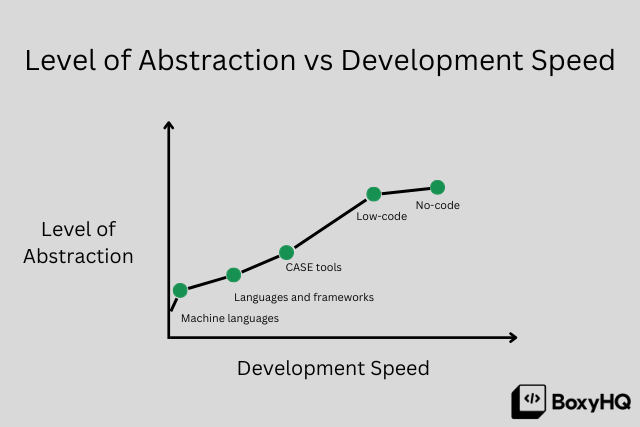
How low-code solutions are changing how we build products and workflows

Marketing Consultant
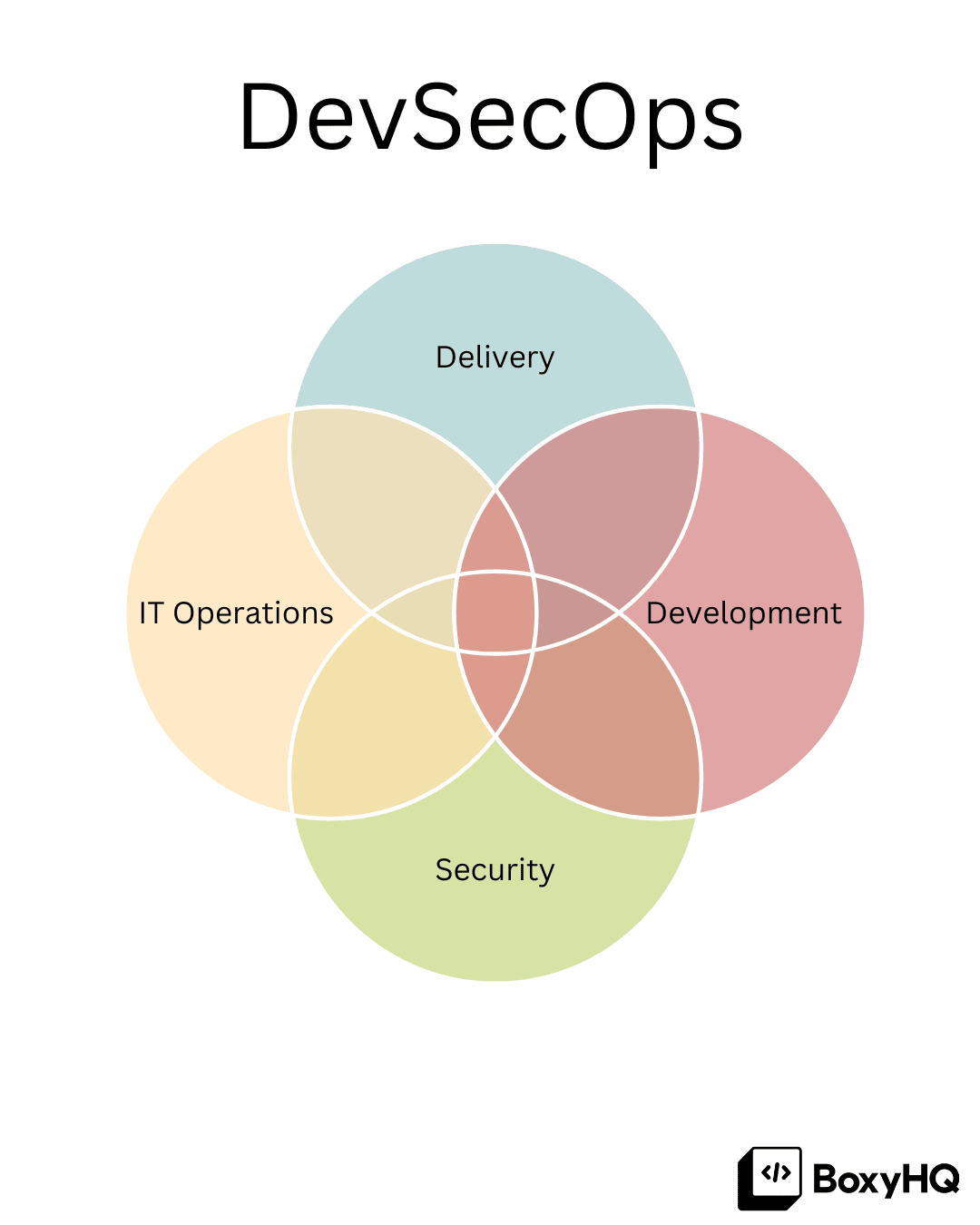
What is DevOps and how has it evolved into DevSecOps

Marketing Consultant
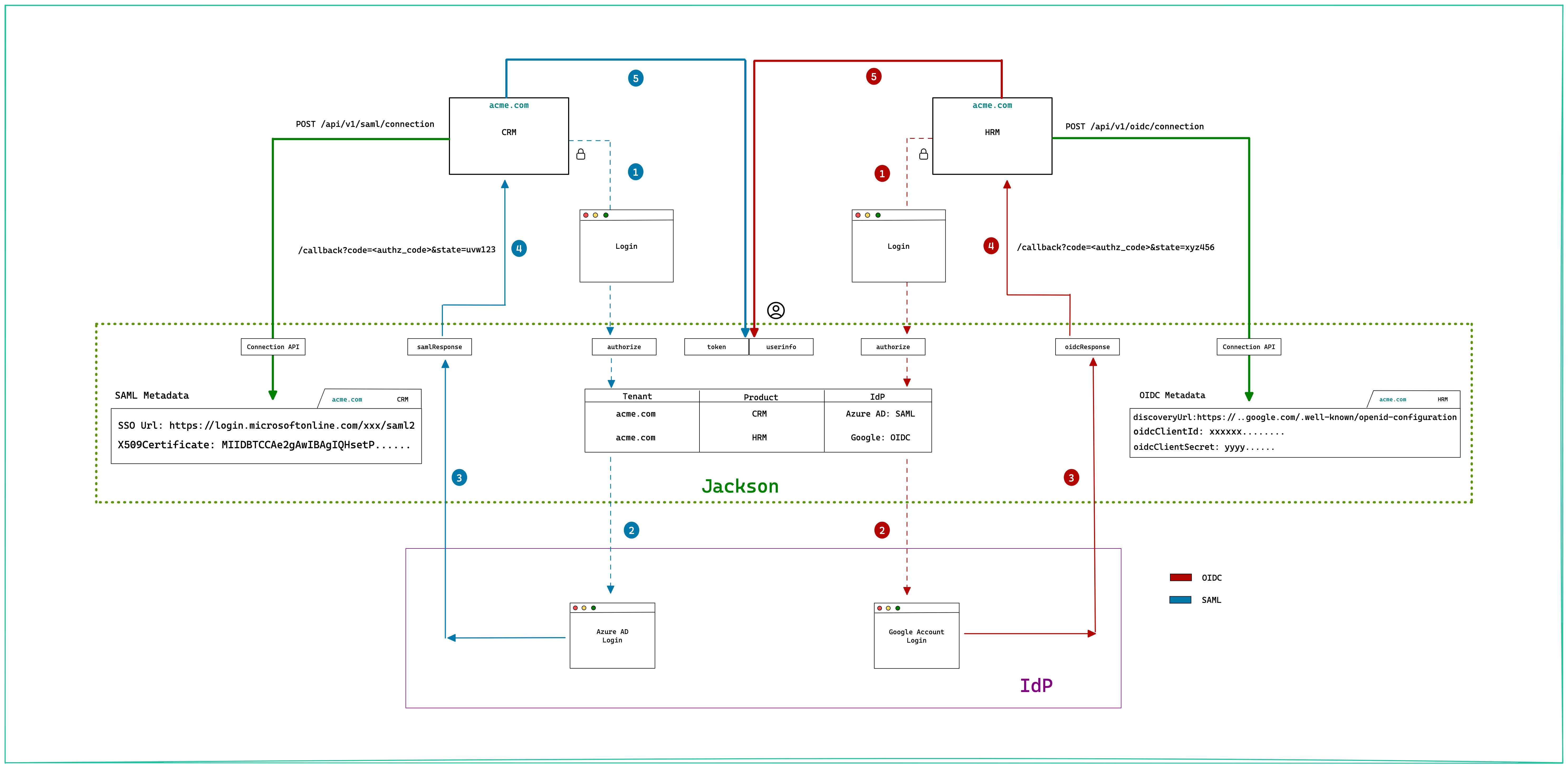
SSO Building blocks - SAML, OAuth 2.0 and OpenID Connect

Senior Developer @BoxyHQ
Enterprise-ready SaaS Starter Kit

Senior Developer @BoxyHQ
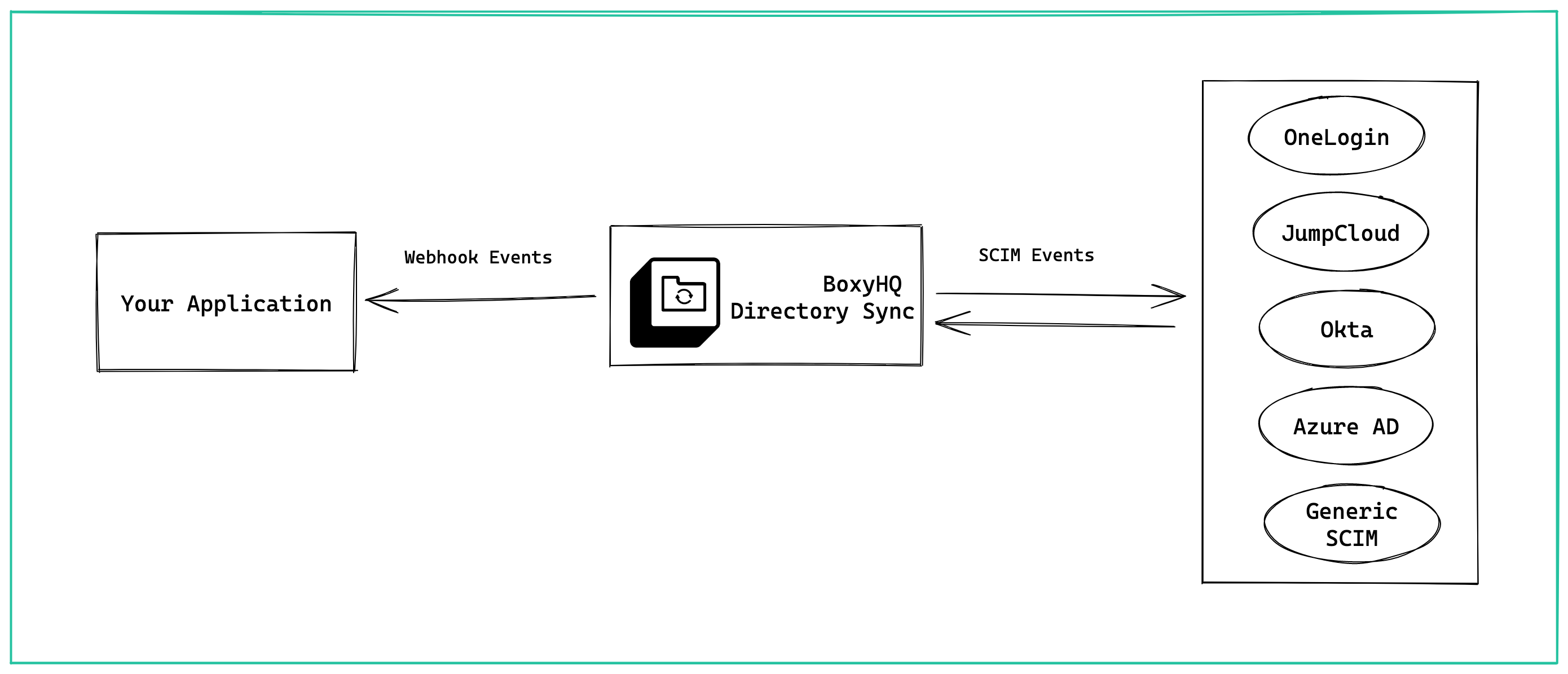
Understanding SCIM and Directory Sync

Senior Developer @BoxyHQ
Be enterprise-ready: Three reasons not to build enterprise features!

Co-founder & COO @BoxyHQ
Understanding SAML SSO, the basics from the solution provider's side

Marketing Consultant
Understanding SAML SSO, the basics from the user side

Marketing Consultant
How to add SAML Single Sign On to an Express app

Senior Developer @BoxyHQ
Benchmarking fluent-bit with Clickhouse

Senior Software Engineer (Open Source Dev Tools) @BoxyHQ
How early-stage startups should sell to enterprises

Co-founder & COO @BoxyHQ
The IKEA effect in Software Engineering

Co-founder & CEO @BoxyHQ
Enterprise Readiness made simple

Co-founder & CEO @BoxyHQ